You can reach us: Via Live Chat, phone, email, or in person.
chat loading…
Current hours are listed at itsupport.maine.edu
Phone Support
207.778.7300
Current hours are listed at itsupport.maine.edu
Email Support
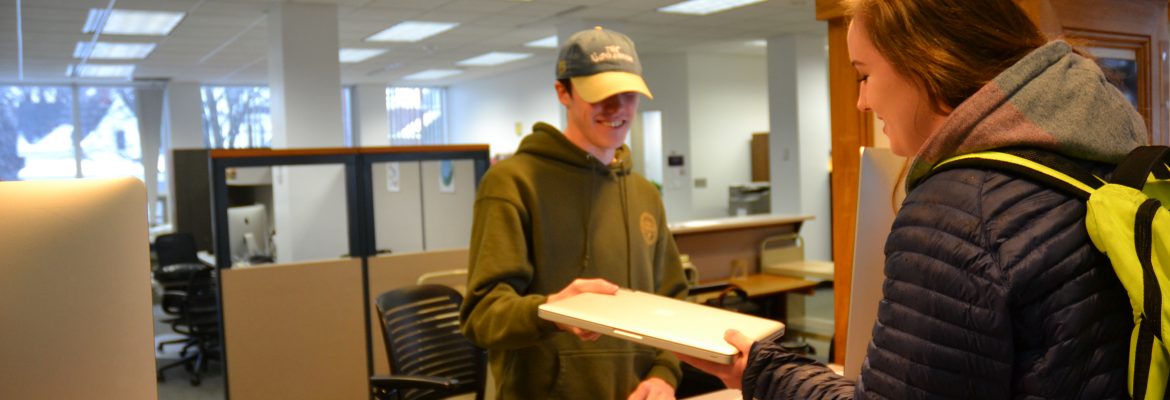
In Person
ACCEPTABLE USE OF INFORMATION AND INFORMATION SYSTEMS
As a student, faculty, or staff member, it is your responsibility to review and understand the Acceptable Use of Information and Information Systems Administrative Practice Letter. It applies to the entire University of Maine System, has been reviewed by key constituents and approved by the Treasurer of the University of Maine System. For questions, please call (207) 581-5846. For links to other University of Maine System APLs, visit https://www.maine.edu/apls/